The growing emphasis on enterprise security has grown in the past few years. Application Whitelisting Tools is an important step in securing your IT infrastructure.
What is Application Whitelisting?
Application whitelisting is the process of indexing, approving, and allowing the application(s) to be present on the computer system.
Unlike in the case of blacklisting where the system blocks an application or set of applications; the process of whitelisting allows a particular set of tools to run on the network.
Application whitelisting is more useful in environments which require individual systems to be more secured, due to data on these systems being highly confidential.
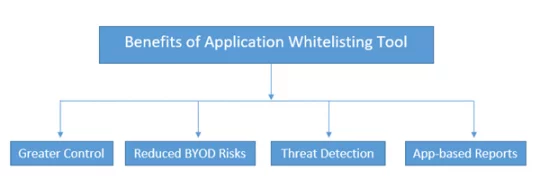
4 Benefits of Application Whitelisting
- Greater Control over the applications
- Reduced risk associated with Bring-Your-Own-Device (BYOD) policies
- Threat Detection, Malware, Trojan Insights
- Application-based reports such as upgrade, usage, and install/uninstall reports
Application whitelisting allows you to have greater control over the type of apps installed inside the network.
In a data-sensitive environment such as government organizations or projects involving sensitive data, this technology proves to be more helpful than application blacklisting.
Application policy feature related to your mobile devices in application whitelisting tools allows you to minimize the risks associated with your own devices and applications installed on them.
Application whitelisting tools provide the insights of cyber threats, the applications through which the malware and/or Trojan viruses penetrate inside a system.
Also, they provide a detailed analysis of these threats in the form of a report which can help you to shortlist, or reassess the whitelisted applications.
Application Whitelisting tools also provide you a detailed application-based report. It helps you to understand the app-based activities such as data usage by an application, new installations of an app on a particular machine, uninstalling of an application from a device.
These tools provide the application upgrade notifications as well to help the organizations to keep up with the latest versions of the applications.
We will be discussing key application whitelisting tools in the succeeding content.
Also Read: 10 Benefits of Mobile Device Management
Scalefusion provides a holistic approach to application whitelisting through its application management feature. Businesses can whitelist trusted apps to run on managed devices and ensure no unauthorized or malicious apps are installed or accessed on these devices. The whitelisted applications can be locked on managed devices to turn them into single or multi-app kiosks, serving only dedicated business purposes. Additionally, using Scalefusion, you can install, update, or uninstall apps silently and remotely without any user intervention.
ThreatLocker Protect offers cutting-edge cybersecurity solutions for firms operating in any industry. The features of Allowlisting and Ringfencing strengthen access management parameters, incorporating enhanced control over the applications, libraries, and scripts within a device or server, blocking malicious and unauthorized software. By allowing or whitelisting only the software individuals need, ThreatLocker restricts every other application and reduces the possibilities of cyber-attacks. The key features of ThreatLocker Application Allowlisting include:
- Deny by default: According to the allowlist, the tool blocks every software that is not included in the list.
- Firewall-like policies: ThreatLocker establishes strong policies that enable enhanced control over the access and blocking of applications.
- Time-based policies: Set a specific timeframe to allow access to any application. After the time is over, the application is automatically blocked.
- Built-in applications: ThreatLocker manages over 8,000 built-in application definitions to ensure a seamless experience for the end user, even if the application updates.
Ringfencing offers granular security controls for approved applications interacting with other applications, files, data, and the network. It creates a security barrier between software and potential threats, even when attackers use powerful tools to access without authentication. The major features of ThreatLocker are:
- Ringfencing mitigates the risks of fileless malware, restricting the functionalities of applications.
- It has granular policies that can stop applications from connecting with other software, storage devices, network resources, and more.
- It restricts what applications can access, eliminating application attack possibilities.
- Ringfencing allows users to choose applications that can access their files.
Applocker whitelisting tool comes with Microsoft windows server editions, and windows operating systems with its enterprise and upgraded editions.
Its rules can apply to an individual or also to a group of systems. You can also customize and set up different levels of enforcement as required.
PowerBroker whitelisting tool is another popular application whitelisting tool that supports Windows, Linux, and Mac too.
This application is considered to have a more application control-based approach. It is more popular due to its key features, such as activity logging and privilege management. Its mobile policy features also help you out with the issues associated with the BYOD policy.
PolicyPak integrates with Windows server and other OS editions mainly. It comes with three main editions, namely Group Edition, Cloud Edition, and MDM Edition. You can also opt for a GP Compliance Reporter tool for whitelisting.
PolicyPak Cloud Edition has a BYOD feature while Group Edition is more suited for smaller organizations.
MDM Edition is similar to Cloud Edition but is useful with existing mobile device management services such as Workspace One, Intune, etc.
This tool is also useful with Windows. Its primary purpose is to keep sensitive data within the environment and help the organizations to secure data with more ease.
It is known for its key features such as hierarchical access, endpoint security, mobile support, and the ability to main the privileges irrespective of locations.
It has other important features, such as monitoring of inactivity, data management, secured installation.
It comes with an upgrade and notification feature for the uninstallation of the application as well.
They provide an application whitelisting tool called Defendpoint, which is popular in practices such as BYOD, enterprise network security, endpoint security, malware detection, and report management.
Centrify Server Suite’s EPM is also a popular application whitelisting tool which focuses more on privilege policies, reporting and auditing, and threat analytics.
Its core features also include application control, application management based on vulnerabilities, and security of ecosystem integration.
Kaspersky's whitelisting tool focuses more on default-deny mode, which helps to block the unauthorized applications easily and notifies the network admin about the same.
It also comes with other key features, such as a local and global whitelisting database to comply with different regional data protection policies.
Also, with a feature like a golden image, you can prioritize the most crucial applications to start and work on the operating systems.
DriveLock is a superior tool that allows enhanced control over your applications. Users can block or unblock any software with this tool that runs on a centralized recording facility. Alongside offering application whitelisting methods, DriveLock also guides employees on how to manage data and external data carriers securely.
The tool also generates customized user notifications and enables central dashboards, which contribute to elevated user experience.
Also Read